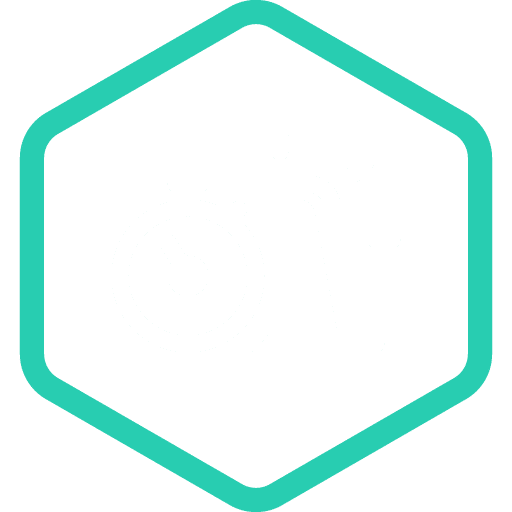
The most common initial attack vectors observed in incidents
The same three attack vectors remained dominant over the past year, increasing their combined share to more than 80% of all observed incidents. As in previous years, data encryption was the most common form of damage resulting from attacks initiated through these vectors.
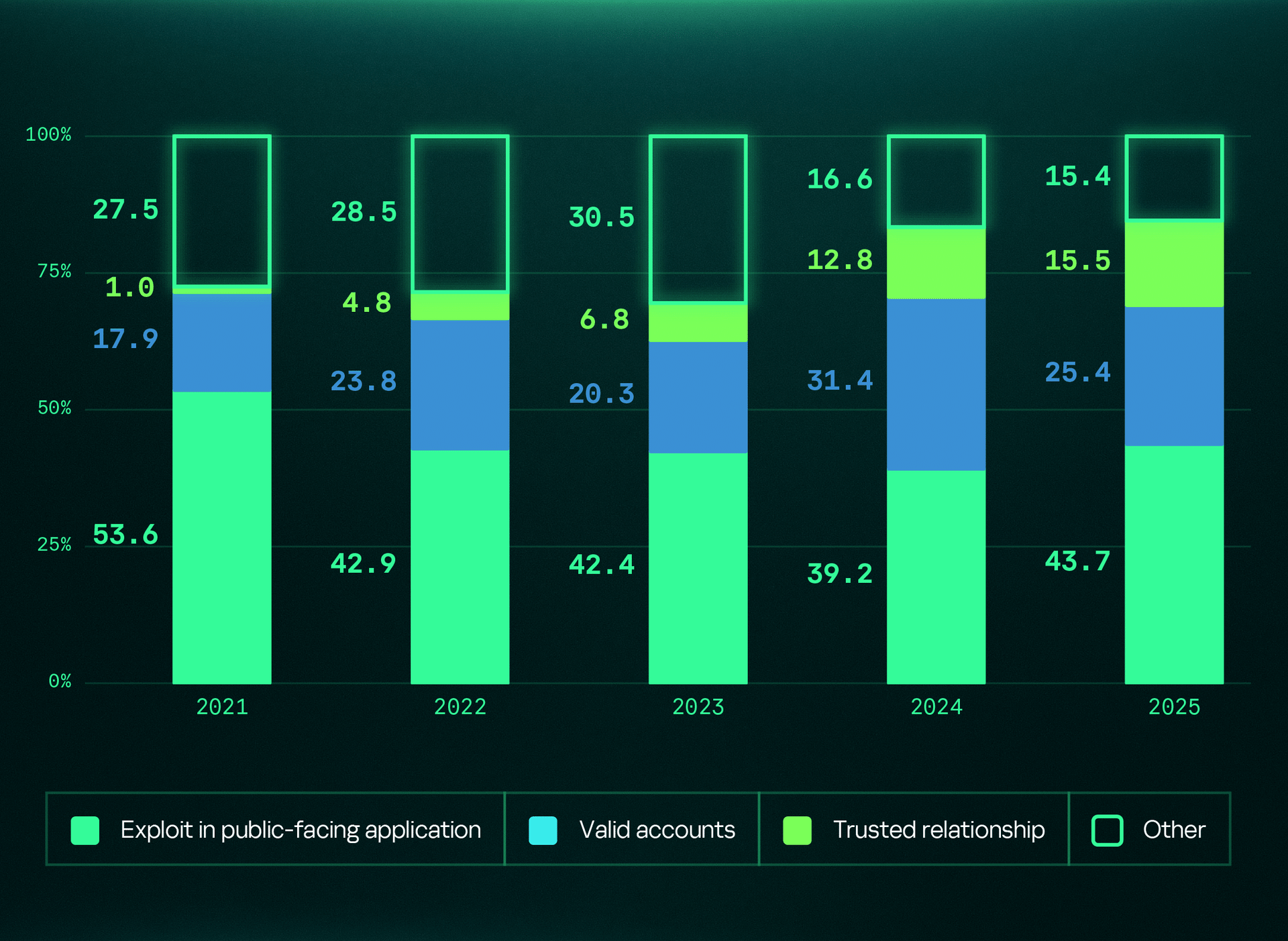
The most common types of high-severity incident at the moment of detection
Human-driven targeted attacks accounted for 24% of high-severity incidents in 2025. While this marks a decline from 2024, they remain the leading cause of high-severity incidents identified in MDR statistics. Despite advances in automated detection tools, determined attackers continue to find ways to evade them. Countering these threats requires human-driven solutions, making Managed Detection and Response a critical approach.
Related services