
Lessons from the Bybit hack: how to store crypto safely
Takeaways for regular crypto holders from the biggest crypto heist in history.
562 articles

Takeaways for regular crypto holders from the biggest crypto heist in history.

What information does an MDR service need to protect a company from complex targeted attacks?

Online converters are a tempting but dangerous way to change file formats. We tell you how to convert files and not get trojanized.

We break down the most covert mechanism of smartphone surveillance using real-life examples.

We’ve discovered apps in the official Apple and Google stores that steal cryptocurrency wallet data by analyzing photos.

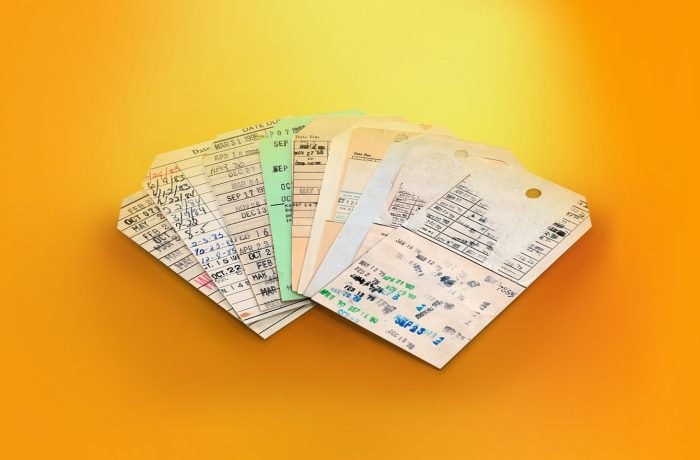
It feels as if spam is as old as the internet itself. The post looks at the money-making scams devised over the years, and how to avoid them today.

What network-security and access-control tools do the world’s top cyber-regulators recommend to companies?
Every file, video, etc. we share contains a lot of hidden additional information — metadata. What’s it for, and is it really necessary?

Our Android apps are no longer available on Google Play. We explain how to download, install, and update them by alternative means.

How to avoid giving away your password to scammers when logging in to third-party sites or viewing “encrypted” or “confidential” documents.

Mistakes to learn from in 2024 – and resolutions for a safer 2025.

Scammers have invented a new trick — they post cryptowallet seed phrases in YouTube comments using newly created accounts. Here’s how it works

The best privacy-focused services that make practical gifts for friends and family.

We explain how to detect if scammers have gained access to your Telegram account, and what to do about it.

Threats to data stored in Sync, pCloud, and other encrypted alternatives to Dropbox.

What IT and cybersecurity leaders need to know about implementing network detection and response.

Hidden logic, data poisoning, and other targeted attack methods via AI systems.

Black Friday is a great opportunity for scammers to line their pockets — but not with your money if you follow our advice.

We’ve updated the design of our password manager’s mobile version. Storing and managing passwords is now even more convenient.

Five dead simple tips to greatly improve your defenses against cybercriminals.