The next page of The Сyberworld Survival Guide. The entire guide can be found here: https://www.kaspersky.com/blog/tag/securityIS
Rocky begins.
The next page of The Сyberworld Survival Guide. The entire guide can be found here: http://www.kaspersky.com/blog/tag/securityIS
The next page of The Сyberworld Survival Guide. The entire guide can be found here: https://www.kaspersky.com/blog/tag/securityIS
Rocky begins.

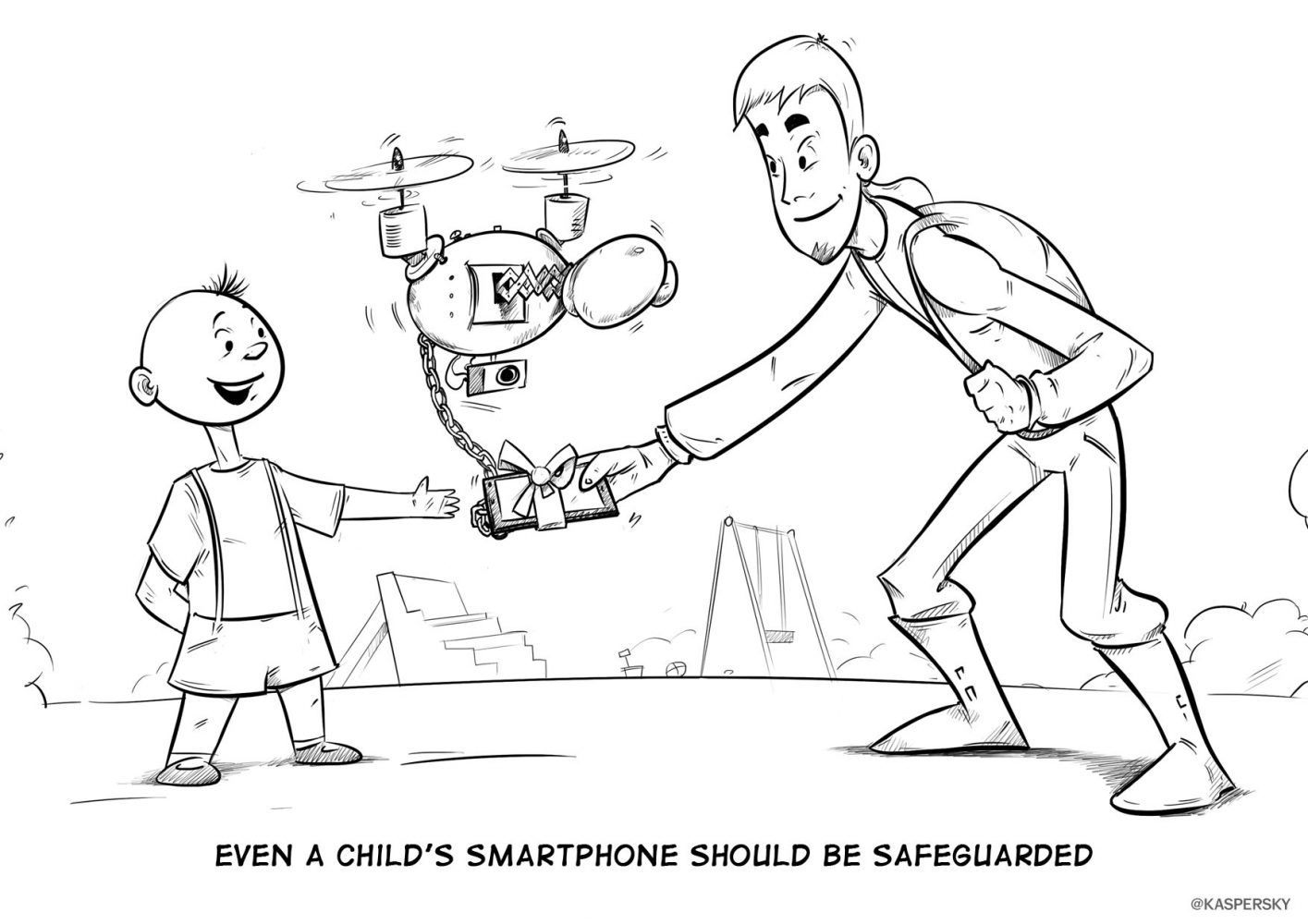
When a computer is operated by a child, it should be protected against a whole new set of threats. Some popular security solutions fail to provide sufficient protection.

The best privacy-focused services that make practical gifts for friends and family.
We explain how to detect if scammers have gained access to your Telegram account, and what to do about it.
Threats to data stored in Sync, pCloud, and other encrypted alternatives to Dropbox.
What IT and cybersecurity leaders need to know about implementing network detection and response.