
Why electronic payments get attacked?
While fast and convenient, electronic payments are a risky matter if not secured properly.
3892 articles

While fast and convenient, electronic payments are a risky matter if not secured properly.

Many would see an aircraft just the way they see a car: should it be 15 or 20 years old, it is automatically perceived as obsolete. This reasoning is misleading.
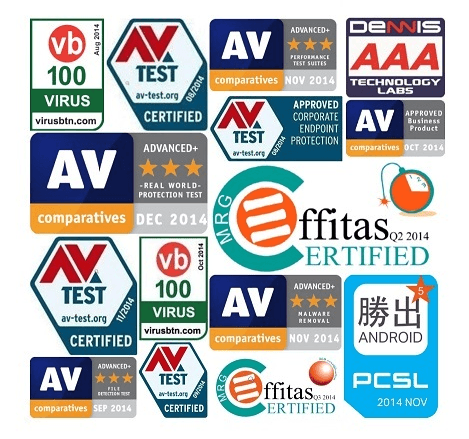
It’s always nice to see high marks and awards from independent testing labs. The latest roundup shows that Kaspersky Lab’s product performance is consistently great over the time.

WhatsApp has finally released a Web version of its popular mobile messaging service. We take a look at it from the security perspective.

“All the things I really like to do are either immoral, illegal, or fattening.” As always, there are exceptions.

The Internet continues to find its way into the private lives of its users. Here, we brief you on the most common methods of online tracking.

Banks continue to lose a lot of money because of carders and seek ways to ensure their customers are safe. Let’s take a look at the latest methods of bank card protection and how they may evolve.

Understanding something means getting the correct answers to questions. In this post, we have picked – and answered – three questions that need to be asked to ensure business data security.

Whether you’re buying or selling a secondhand Apple device, you can be fooled by criminals. We have gathered tips on how to minimize your chances of being taken by such frauds.

It can be hard for businesses to keep in mind everything they need to do to be protected. We have identified five trends in cybersecurity that are affecting businesses, directly or indirectly, at a formidable level.

As is, a QR code can quickly take you to a site or another resource but not necessarily to the one you really want to visit. Thus Kaspersky Lab offers a free and safe QR scanner!

Have you ever wondered how a typical office would look in a decade or so? Allow us to take you on a small tour of the most interesting office concepts.

With Kaspersky Small Office Security there’s no need to waste a lot of time ensuring your business is a cyber safe environment.

In part one of our series, we discussed tech used by bank card ‘seekers’. Today, we’ll cover how criminals carry out the most dangerous skimming processes.

“A single cyberincident can kill a business” may sound like an exaggeration, but it is not. In this blog post we prove it with two different stories.

New version of CTB-Locker, a ransomware that uses Tor and Bitcoin to evade detection and takedowns, should be avoided at all costs.

What is the best way to start assessing your company’s cybersecurity issues? First, look around at what you have.

The top privacy data leaks in 2014 include: data breaches at Target and Home Depot, hacks of JP Morgan and Barclays banks, and leaks at Orange and Dropbox.

As part of its Project Zero security initiative, Google disclosed a few vulnerabilities in Windows, some ahead of a planned patch. Google simply adhered to its “publicize in 90 days after private vendor disclosure” policy, but where are end users’ interest in this “game of flaws”?

Researcher discovers that Progressive Snapshot tools lack any real security controls and could be exploited by attackers to hack cars.

As a student, I had a part-time job offering PC support services. Now, when visiting relatives who aren’t good at servicing their computers, I often have to apply my expertise once again.