Lazarus’ key operation – “Operation DreamJob” – continues to evolve with new sophisticated tactics that have persisted for more than five years, according to Kaspersky's Global Research and Analysis Team. The latest targets include employees from a nuclear-related organization, who were infected via three compromised archive files appearing to be skill assessment tests for IT professionals. This ongoing campaign leverages a range of advanced malware, including a newly discovered modular backdoor, CookiePlus, that was disguised as open-source plugin.
Kaspersky’s GReAT discovered a new campaign linked to the infamous Operation DreamJob, also known as DeathNote, a cluster associated with the notorious Lazarus group. Over the years, this campaign has evolved significantly, initially emerging in 2019, with attacks targeting worldwide cryptocurrency-related businesses. During 2024, it has expanded to target IT and defense companies across Europe, Latin America, South Korea, and Africa. Kaspersky’s latest report provides new insights into a recent phase of their activity, revealing campaign targeting employees working at the same nuclear-related organization in Brazil as well employees of an unidentified sector in Vietnam.
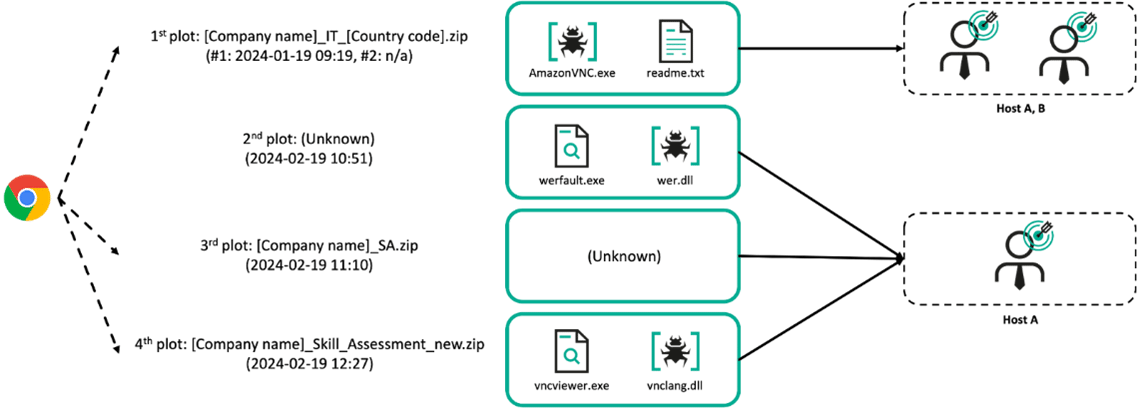
Over the span of one month, at least two employees from the same organization were targeted by Lazarus, receiving multiple archive files disguised as skill assessments for IT positions at prominent aerospace and defense companies. Lazarus initially delivered the first archive to Hosts A and B within the same organization, and after a month, attempted more aggressive attacks on the first target. They likely used job search platforms like LinkedIn to deliver the initial instructions and gain access to the targets.
Lazarus has evolved its delivery methods and improved persistence through a complex infection chain involving various types of malware, such as a downloader, loader, and backdoor. They launched a multi-stage attack using trojanized VNC software, a remote desktop viewer for Windows, and another legitimate VNC tool to deliver malware. The first stage involved a trojanized AmazonVNC.exe, which decrypted and executed a downloader called Ranid Downloader to extract internal resources of the VNC executable. A second archive contained a malicious vnclang.dll that loaded MISTPEN malware, which then fetched additional payloads, including RollMid and a new variant of LPEClient.
Route of malicious files created on victims host
Additionally, they deployed an unseen plugin-based backdoor which GReAT experts dubbed CookiePlus. It was disguised as ComparePlus, an open-source Notepad++ plugin. Once established, the malware collects system data, including the computer name, process ID, and file paths, and makes its main module “sleep” for a set amount of time. It also adjusts its execution schedule by modifying a configuration file.
“There are substantial risks including data theft, as Operation DreamJob gathers sensitive system information
that could be used for identity theft or espionage. The malware’s ability to
delay its actions allows it to evade detection at the moment of penetration and persist longer on the system. By
setting specific execution times, it can operate at intervals that might avoid
being noticed. Additionally, the malware could manipulate system processes,
making it harder to detect
and potentially leading to further harm or exploitation of the system,” comments Sojun Ryu, security expert at Kaspersky’s
Global Research and Analysis Team.
Learn more about new Lazarus campaign at Securelist.com.
About the Global Research and Analysis Team
Established in 2008, Global Research & Analysis Team (GReAT) operates at the very heart of Kaspersky, uncovering APTs, cyber-espionage campaigns, major malware, ransomware, and underground cyber-criminal trends across the world. Today GReAT consists of 35+ experts working globally – in Europe, Russia, Latin America, Asia, Middle East. Talented security professionals provide company leadership in anti-malware research and innovation, bringing unrivaled expertise, passion and curiosity to the discovery and analysis of cyberthreats.
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. With over a billion devices protected to date from emerging cyberthreats and targeted attacks, Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection, specialized security products and services, as well as Cyber Immune solutions to fight sophisticated and evolving digital threats. We help over 200,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
