Attackers behind a recent surge in phishing and payment-interception attacks on industrial companies are also stealing victims’ project and operational plans, as well as diagrams of electrical and information networks, according to a report by Kaspersky Lab’s Industrial Control Systems Cyber Emergency Response Team.
Attackers behind a recent surge in phishing and payment-interception attacks on industrial companies are also stealing victims’ project and operational plans, as well as diagrams of electrical and information networks, according to a report by Kaspersky Lab’s Industrial Control Systems Cyber Emergency Response Team. Such information is not required for the attackers’ primary money-making scheme, and it raises a number of worrying questions about the cybercriminals’ future intentions.
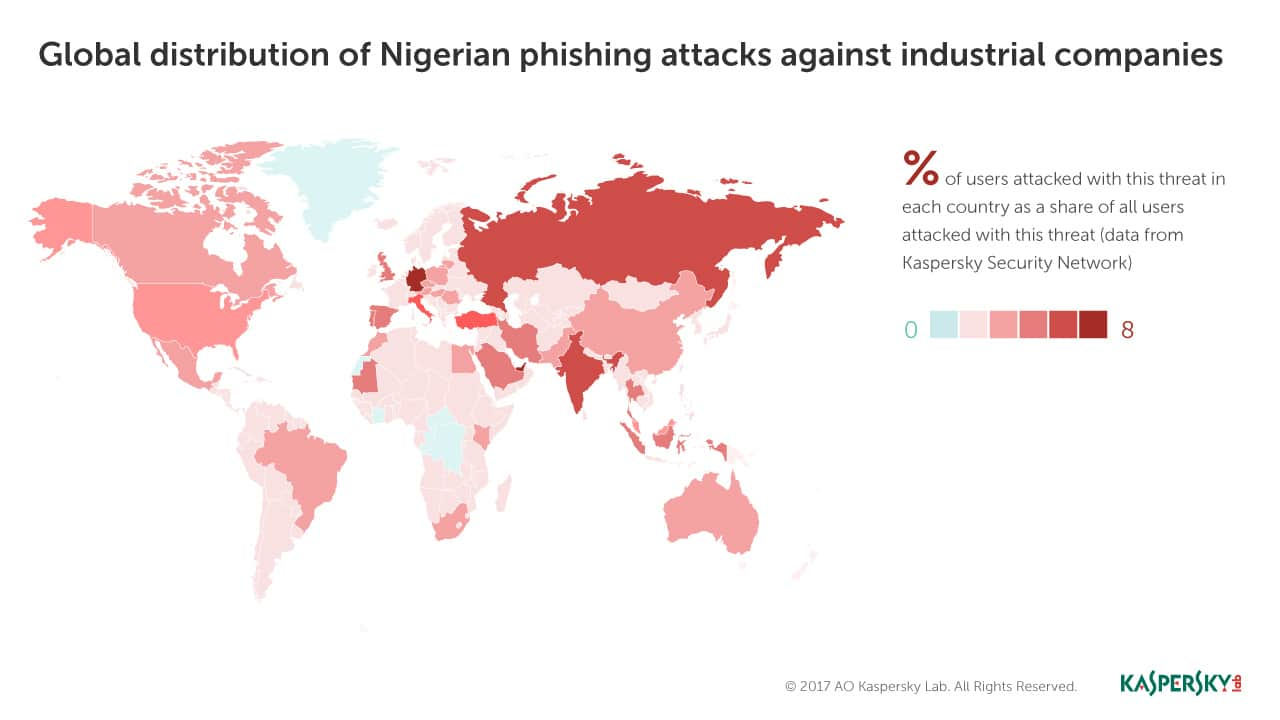
Business Email Compromise (BEC) attacks, often linked to Nigeria, seek to hijack genuine business accounts which the attackers can monitor for financial transactions to intercept or redirect. In October 2016, Kaspersky Lab researchers noticed a significant spike in the number of malware infection attempts targeting industrial customers. They identified over 500 attacked companies in 50 countries, mainly industrial enterprises and large transportation and logistics corporations. The attacks are ongoing.
The attack sequence
The attack sequence begins with a carefully crafted phishing email, appearing to come from suppliers, customers, commercial organizations and delivery services. The attackers use malware belonging to at least eight different Trojan-spy and backdoor families, all available cheaply on the black market, and designed primarily to steal confidential data and install remote administration tools on infected systems.
On infected corporate computers, the attackers take screenshots of correspondence or redirect messages to their own mail box so they can look out for interesting or lucrative transactions. The payment is then intercepted through a classic man-in-the-middle attack, by replacing the account details in a legitimate seller’s invoice with the attackers’ own. It can be difficult for a victim to spot the substitution until it is too late and the money has gone.
The unknown threat
While analyzing the command-and-control servers used in the most recent, 2017, attacks, the researchers noted that screenshots of operations and project plans, as well as technical drawings and network diagrams were among the data stolen. Further, these images had not been taken from the computers of project managers or procurement managers, the attackers’ usual targets, but from those belonging to operators, engineers, designers and architects.
“There is no need for the attackers to collect this kind of data in order to perpetrate their phishing scams. So what do they do with this information? Is the collection accidental, or intentional – perhaps commissioned by a third party? So far, we have not seen any of the information stolen by Nigerian cybercriminals on the black market. However, it is clear that, for the companies being attacked, in addition to the direct financial loss, a Nigerian phishing attack poses other, possibly more serious, threats,” said Maria Garnaeva, Senior Security Researchers, Critical Infrastructure Threat Analysis, Kaspersky Lab.
The next step could be for attackers to gain access to the computers that form part of an industrial control system, where any interception or adjustment of settings could have a devastating impact.
Attacker profile
When the researchers extracted the command and control (C&C) addresses from the malicious files, it turned out that in some cases the same servers were used for malware from different families. This suggests there is either just one cybercriminal group behind all the attacks, making use of different malware, or a number of groups cooperating and sharing resources.
The researchers also found that most domains were registered to residents of Nigeria.
How to mitigate the threat
Kaspersky Lab advises companies to implement the following basic security best practice:
- Educate employees in essential email security: not clicking on suspicious links and attachments and carefully checking the origin of an email – and keep them informed of the latest tools and tricks used by cybercriminals.
- Always double-check requests to change bank account details, payment methods etc. during transactions.
- Install a security solution on all workstations and servers where possible – and implement all updates without delay.
- In the event of a system being compromised, change the passwords for all accounts used on that system.
- If your organization has an industrial control system, install specialist security that will monitor and analyze all network activity and more.
For more information on this threat, and how to protect against it, read the report on Securelist.com.
For further information on threats facing industrial control systems, visit the ICS CERT.